Monitoring & Threat Detection
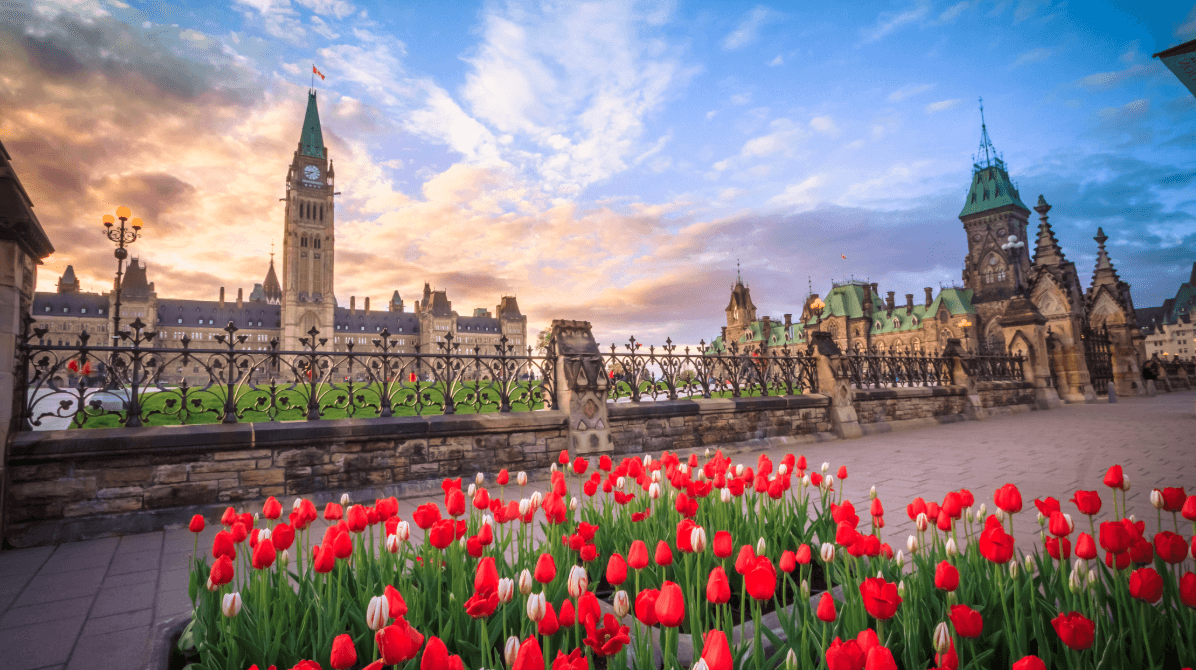
Reduce breach risk by identifying attacker activity early through continuous monitoring of endpoint behavior, identity activity, network traffic, and cloud telemetry. Powered by our SOC in Ottawa and the CrowdStrike platform, we investigate suspicious patterns, validate real threats, and support containment decisions before attackers can move deeper into the environment.
Explore Monitoring & Threat Detection